On the previous article we’ve discuss step by step on how to install and configure MySQL 8.0 database server on Red Hat Enterprise Linux 8.5 (RHEL). However, we need to have secure and harden environment or ecosystem in order to run the web applications, either it personal blog, corporate website or online store.
Well, today we will guide you on how to create secure environment for MySQL 8.0.29 on RHEL machine. We will securing and hardening the installation of MySQL 8.0. But before doing it make sure to meet the following requirenments.
PREREQUISITES:
* VPS, Cloud or Bare-Metal Server. * Running under Operating System Red Hat Enterprise Linux 8.5 (RHEL) * Server IPv4 Address with Superuser Privileges (Root Access) * Gnome Terminal for Linux Desktop * PuTTy SSH Client for Windows or Mac * Powershell for Windows 10/11 * Familiar with DNF and YUM Commands * Must have MySQL 8.0 running on the machine
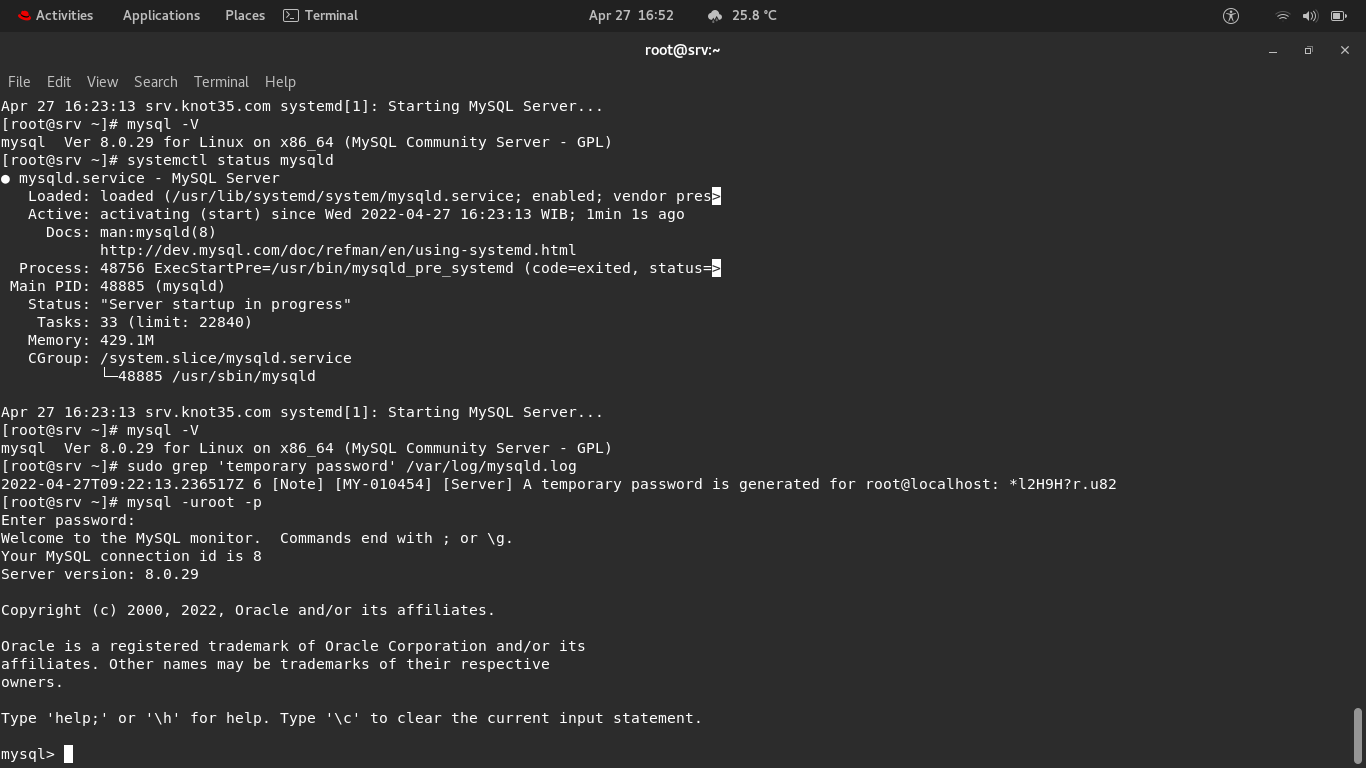
1.) Temporary Root Password for MySQL Administrative Account (Superuser Privileges)
After we have successfully installing MySQL 8.0 on Red Hat Enterprise Linux 8.5 (RHEL machine), you will know the fact that there is no proper root account password setting up on MySQL 8.0. So it’s horible to run MySQL server without knowing the proper root MySQL password.
There is only Temporary MySQL Root Password which you can check and verify using the following command.
$ sudo grep 'temporary password' /var/log/mysqld.log 2022-04-27T09:22:13.236517Z 6 [Note] [MY-010454] [Server] A temporary password is generated for root@localhost: *l2H9H?r.u82
As you can see above that temporary root password for my MySQL administrative account (superuser privileges) is *l2H9H?r.u82. And it mean the temporary password is stored in mysqld.log file under /var/log/ directory.
2.) How to Change the Root Password on MySQL 8.0?
Actually there are many ways to change the root password for MySQL administrative account (superuser privileges) on MySQL 8.0. Well, after knowing temporary root password, simply change the MySQL root password as soon as possible using the following command.
Login to MySQL CLI
$ mysql -uroot -p Enter password: Welcome to the MySQL monitor. Commands end with ; or \g. Your MySQL connection id is 8 Server version: 8.0.29 Copyright (c) 2000, 2022, Oracle and/or its affiliates. Oracle is a registered trademark of Oracle Corporation and/or its affiliates. Other names may be trademarks of their respective owners. Type 'help;' or '\h' for help. Type '\c' to clear the current input statement. mysql>
Change the MySQL Root Password
mysql> ALTER USER 'root'@'localhost' IDENTIFIED BY 'MyNewPass4!';
NOTE: Make sure to replace MyNewPass4! with your new MySQL root password. For example:
mysql> ALTER USER 'root'@'localhost' IDENTIFIED BY 'psht1922#!'; Query OK, 0 rows affected (1.37 sec) mysql>
Then, exit from MySQL CLI:
mysql> exit Bye
3.) Verify a New Root Password for MySQL 8.0
After that you have to verify that your newly created MySQL root password is correct and you can use it to login into the MySQL CLI (Command-Line Interface).
$ mysql -uroot -p Enter password: Welcome to the MySQL monitor. Commands end with ; or \g. Your MySQL connection id is 9 Server version: 8.0.29 MySQL Community Server - GPL Copyright (c) 2000, 2022, Oracle and/or its affiliates. Oracle is a registered trademark of Oracle Corporation and/or its affiliates. Other names may be trademarks of their respective owners. Type 'help;' or '\h' for help. Type '\c' to clear the current input statement. mysql>
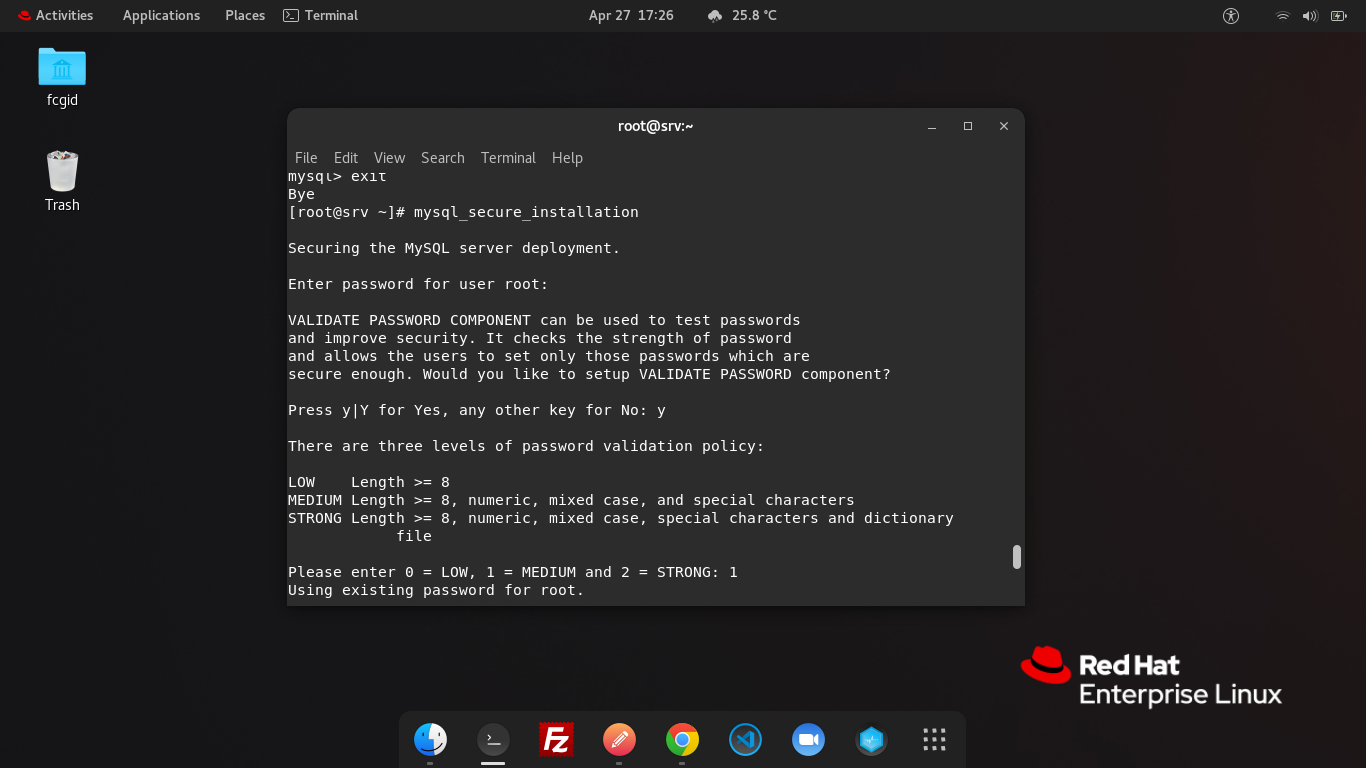
4.) Securing and Hardening MySQL 8.0 Installation
Next, we must securing and hardening MySQL 8.0 Installation on your Red Hat Machine. Simply run the following command to run MySQL Secure Installation. Make sure to select NO if you asked to change the MySQL root password.
$ mysql_secure_installation $ Securing the MySQL server deployment. Enter password for user root: VALIDATE PASSWORD COMPONENT can be used to test passwords and improve security. It checks the strength of password and allows the users to set only those passwords which are secure enough. Would you like to setup VALIDATE PASSWORD component? Press y|Y for Yes, any other key for No: y There are three levels of password validation policy: LOW Length >= 8 MEDIUM Length >= 8, numeric, mixed case, and special characters STRONG Length >= 8, numeric, mixed case, special characters and dictionary file Please enter 0 = LOW, 1 = MEDIUM and 2 = STRONG: 1 Using existing password for root. Estimated strength of the password: 50 Change the password for root ? ((Press y|Y for Yes, any other key for No) : n ... skipping. By default, a MySQL installation has an anonymous user, allowing anyone to log into MySQL without having to have a user account created for them. This is intended only for testing, and to make the installation go a bit smoother. You should remove them before moving into a production environment. Remove anonymous users? (Press y|Y for Yes, any other key for No) : y Success. Normally, root should only be allowed to connect from 'localhost'. This ensures that someone cannot guess at the root password from the network. Disallow root login remotely? (Press y|Y for Yes, any other key for No) : y Success. By default, MySQL comes with a database named 'test' that anyone can access. This is also intended only for testing, and should be removed before moving into a production environment. Remove test database and access to it? (Press y|Y for Yes, any other key for No) : y - Dropping test database... Success. - Removing privileges on test database... Success. Reloading the privilege tables will ensure that all changes made so far will take effect immediately. Reload privilege tables now? (Press y|Y for Yes, any other key for No) : y Success. All done! [root@srv ~]#
CONCLUSION:
You have successfully in securing and hardening environment for MySQL 8.0 database server which run on Red Hat Enterprise Linux 8.5 (RHEL), as well as create the correct root password. Well, now you have secure ecosystem, so you can use it later to manage your web application without any big issues.